in today's internet era, cloud servers have become the preferred solution for building corporate and personal websites. in particular, hong kong cloud servers have attracted the attention of a large number of users with their superior network environment and stability. this article will delve into the reasons and applications of choosing hong kong cloud server cn2 2 core 2g to help you better understand the advantages of this product and its suitable usage scenarios.
due to its unique geographical location, hong kong cloud servers have high-quality network infrastructure and stable international bandwidth, which are particularly suitable for business needs in mainland china and the asia-pacific region. by choosing hong kong cloud server cn2 2 core 2g, you can not only enjoy low-latency and high-speed network connections, but also effectively improve user access experience. in addition, the flexibility and scalability of hong kong cloud servers allow enterprises to adjust resources at any time according to actual needs, reducing operating costs.
the cn2 line is a high-performance network line launched by china telecom to improve the quality of international bandwidth. choosing hong kong cloud server cn2 2 core 2g means that you will be able to enjoy a more stable and faster network connection. the cn2 line performs well in international data transmission, especially when accessing domestic websites. it has low packet loss rate and small delay, which can effectively improve access speed. this is especially important for companies that need to interact frequently with mainland users.
hong kong cloud server cn2 2 core 2g configuration is suitable for the needs of small and medium-sized enterprises, startups and personal websites. for applications that consume relatively few resources, such as corporate official websites, blogs, and small e-commerce platforms, a 2-core 2g configuration is particularly suitable. this configuration not only ensures basic operational requirements, but also provides sufficient performance support while avoiding waste of resources. as your business develops, you can easily expand capacity to meet growing needs.
one of the most important factors when choosing hong kong cloud server cn2 2 core 2g is its performance and stability. the 2-core processor can support multi-threaded tasks and is suitable for handling concurrent requests, while the 2gb of memory is enough to handle general application loads. combined with the advantages of cn2 lines, this configuration can maintain good response speed even during peak hours. in addition, cloud service providers in hong kong usually provide 7x24-hour technical support to ensure that problems can be solved in a timely manner, further improving the stability of the service.
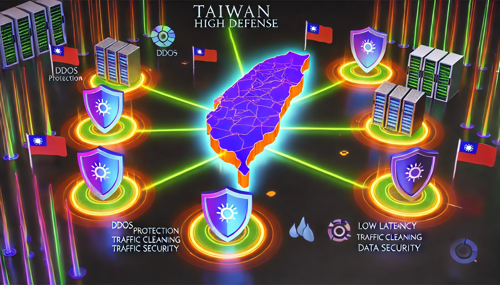
when choosing a cloud server, security is a factor that cannot be ignored. hong kong cloud server cn2 2 core 2g is usually equipped with modern security protection measures, including firewall, ddos protection and data backup. these measures can effectively protect your data security and prevent potential cyber attacks. in addition, hong kong's legal environment is relatively friendly in terms of data privacy, which can provide users with better data protection guarantees and make users feel more at ease when using it.
when choosing hong kong cloud server cn2 2 core 2g, it is crucial to choose the right cloud service provider. first, you need to evaluate its network infrastructure, quality of service, and level of technical support. secondly, looking at user reviews and case studies can help you understand its actual use. finally, pay attention to the terms in the service contract to ensure there are no hidden fees and a reasonable refund policy to protect your rights.
to sum up, choosing hong kong cloud server cn2 2 core 2g is a wise choice, especially suitable for small and medium-sized enterprises and individual users. its superior network environment, stable performance and security guarantee make it an ideal choice for business growth. when choosing, be sure to choose a reputable service provider based on your own needs to ensure you get the best service experience. i hope this article can provide you with valuable reference when choosing a cloud server.
- Latest articles
- Practical advice on improving rankings for American website clusters through content and technology
- Does Battlefield 5 have Vietnamese servers? Compare the connection advantages and disadvantages with servers in neighboring countries
- Analysis of the Deployment and Advantages of Native Vietnamese and Hong Kong IPs in the Interconnection of Hong Kong and Vietnam Businesses
- Practical methods for low-cost implementation of Hulu VPS traffic forwarding in the United States
- Explanation of technical details for building exclusive Korean-origin IPs, including NAT routing and port mapping settings
- Considerations for cloud servers in Singapore include backup strategies and disaster recovery plans
- German paper airplane server setup guide: From zero configuration to stable operation, a complete walkthrough
- Qualifications and technical specifications that must be verified when choosing a US server hosting intermediary
- Purchasing Guide: Price Ranges and Depreciation Methods for Advantech Servers in Taiwan
- Recommended tutorial videos to help you get started from scratch managing the Scum Malaysia server environment
- Popular tags
-
hong kong pccw native ip performance optimization suggestions in high concurrency scenarios
for the performance optimization suggestions of hong kong pccw native ip in high concurrency scenarios, we provide practical solutions and precautions from the aspects of network architecture, load balancing, connection management, caching and monitoring. -
Market price analysis and purchasing guide for Hong Kong native IP
This article analyzes the market price of native IP in Hong Kong and provides a purchasing guide to help users understand market trends and choose appropriate services. -
legal advisors suggest key items that companies should pay attention to when signing hong kong station cluster leasing regulations
legal advisors suggest that companies should pay attention to key items such as contract subject matter, data protection, intellectual property rights, service levels, breach of contract and dispute resolution when signing hong kong station cluster leasing regulations to reduce legal and operational risks.


